
Lighting control today: the uncomfortable truth
Many buildings rely on legacy systems that sit on the network, unmanaged and insecure. They rarely meet modern cyber requirements or insurance expectations.
- Single shared passwords with no access control or audit trail.
- Unpatched head-end PCs or controllers running old Windows or Linux versions.
- TeamViewer / RDP left open for remote access, often without IT oversight.
- No backups and no recovery plan if the machine fails or is stolen.
The hidden problems with traditional lighting control systems
After practical completion, lighting control is often out of sight and out of mind. The system keeps running, but it may no longer be controlled, monitored or secured. Over time this creates real cyber, operational and insurance risks for the building owner and occupier.
Access & security
Single shared passwords and uncontrolled access
Many systems use one site-wide password. It is emailed, written down and shared with contractors and tenants.
No per-user accounts or roles.
No activity logging or change history.
Ex-employees often still know the password.
Passwords are sometimes stored in plain text in job folders or emails.
Remote access
Uncontrolled TeamViewer / RDP / VPN access
To allow support, many sites have TeamViewer, LogMeIn, RDP or similar permanently enabled on the head-end PC.
Remote access is often outside IT’s normal controls.
Opens a direct path from the internet into the building network.
Difficult to track who connected and what was changed.
The addition of network dongles or internet connections direclty on the Server or embedded controllers without IT’s knowledge
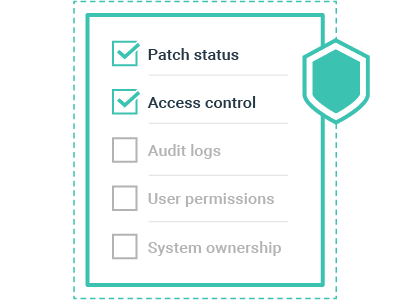
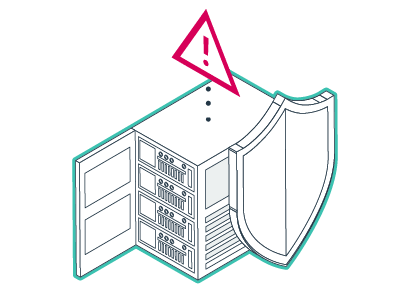
Compliance & insurance
Systems that do not meet cyber insurance obligations
Many cyber insurance policies require that servers are:
Under current warranty or support.
Patched within a defined timeframe after updates are released.
Protected with user authentication and access control.
A forgotten, out-of-support head-end PC or controller can become an unmanaged attack vector that may jeopardise cover.
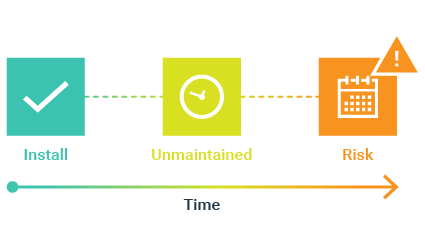
Lifecycle & maintenance
Outdated, unmaintained hardware and software
Lighting servers or controllers are often:
Running unsupported versions of Windows, Linux or Windows CE.
No longer under warranty or hardware support.
Rarely patched or monitored by IT.
Sharing networks with HVAC, lifts, fire and other critical systems.
Contractors working on other services may introduce internet or external connections or otherwise expose the network.
High likelihood of exposure over the building’s service life.
User management
No user offboarding, no audit trail
When staff or contractors leave, their access to lighting control is rarely revoked.
- Default passwords and IP addresses remain unchanged for years.
- No clear record of who has access or what they can do.
- No simple way to reverse accidental or malicious changes.
Backups & resilience
No backups, no recovery plan
Lighting systems are rarely backed up in line with IT policy.
Projects and configuration files often live on a single PC.
Stolen, damaged or corrupted machines cause long outages.
Recovery can be costly and slow, if it is possible at all.
Threat protection
Limited antivirus and phishing protection
Many legacy systems (controllers and servers):
Do not run up-to-date endpoint protection.
Are not actively monitored for threats.
May be vulnerable to malware arriving via email, USB or the network.
Operational risk
IT’s nightmare: “mystery” control systems on the network
Installers, consultants and owners are often unaware of the real design of the control system:
Unknown embedded controllers or mini PCs with outdated OSs.
No clear owner responsible for patching and support.
No documentation of network dependencies or ports.
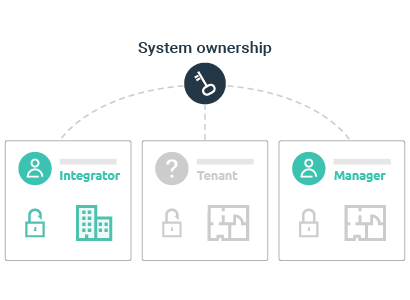
How zencontrol cloud removes these issues by design
Instead of each site running its own fragile head-end PC, zencontrol cloud delivers lighting control as a managed, secure platform. Access, monitoring, logging and updates are built in – not bolted on afterwards.

Traditional on-prem lighting control
- Single shared password for the whole site.
- Uncontrolled TeamViewer / RDP access to a site PC.
- Out-of-support Windows, Linux or Windows CE servers.
- No central audit trail or change history.
- No formal backups or disaster recovery.
- Unclear ownership between facilities, contractors and IT.

zencontrol cloud lighting control
- Role-based user accounts with granular permissions.
- No need for open remote desktop tools on site PCs.
- Cloud-managed platform maintained and updated by zencontrol.
- Activity logging and traceable change history.
- Centralised storage and managed backups of site configuration.
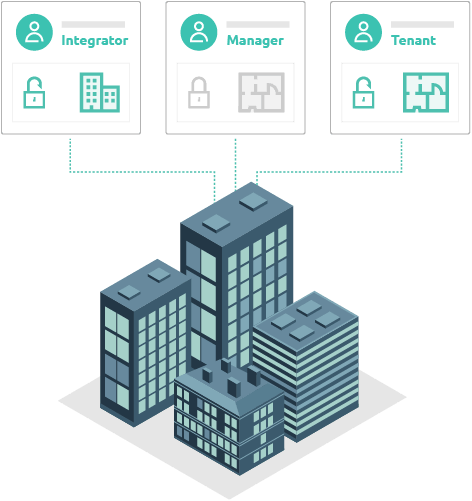
- Clear shared model between building owner, installer and IT.
Key capabilities of zencontrol cloud
zencontrol cloud is designed to address the real-world issues faced by consultants, installers and building owners – not just control lights.
Secure user access control
Move from “one password per site” to controlled, individual access.
- Per-user accounts instead of shared site logins.
- Configurable roles and permissions for different user types.
- Activity logs to see who changed what and when.
- Supports simple removal of access when personnel change.
Designed to support cyber insurance requirements
Many policies require modern patching, supportability and authentication.
- Platform maintained and updated by zencontrol.
- Removes reliance on a forgotten, unsupported local server.
- Provides user authentication and access control.
No exposed remote desktop on site
Remove the need for permanent TeamViewer, LogMeIn or RDP on head-end machines.
- Control is via a secure cloud platform, not a single site PC.
- Access can be managed through existing IT processes.
- Reduces open inbound paths from the internet into the building network.
Lifecycle and patch management handled for you
Lighting control should not depend on an aging PC in a comms room.
- Cloud-based software lifecycle managed by zencontrol.
- Removes the need to schedule OS upgrades on site machines.
- Reduces risk of running unsupported OSs such as old Windows or Linux distributions.
Built-in backup and change recovery
Avoid the cost and downtime of rebuilding a lost or corrupted system from scratch.
- Configuration stored in the cloud, not only on a single PC.
- Ability to roll back or unwind unwanted changes using logs and history.
- Supports alignment with corporate backup and recovery expectations.

Clear ownership and visibility for IT
Make lighting control a known, managed application on the network.
- Documented, predictable architecture instead of unknown boxes.
- Easier for IT to assess, approve and monitor.
- Supports segmentation away from other critical systems where required.
Security and governance by design
zencontrol cloud is built to make doing the secure, compliant thing the easiest option for all parties – consultants, installers, building owners and IT.
- Access based on people and roles, not shared passwords.
- Logging so that changes are attributable and reversible.
- Central management instead of ad-hoc remote access tools.
- Regular platform updates to address security issues.
What this means in practice
When the project is handed over, the building owner receives a system that fits neatly into modern cyber, insurance and IT expectations – rather than a legacy control PC that no one wants to own.
- Supports cyber insurance controls
- Simplifies IT security reviews
- Reduces attack surface
- Improves operational resilience
Result: lighting control is no longer a forgotten box on the network – it becomes a governed, visible part of the building’s digital infrastructure.

For consultants: specify out the risk, not just the hardware
Once a project is handed over, consultants have limited control over how the system is maintained. By specifying zencontrol cloud, you can:
- Reduce reliance on on-site head-end PCs that later fall out of support.
- Provide a clear answer to questions about security, access and updates.
- Align your specification with clients’ cyber and insurance expectations.
- Document an architecture that IT can understand and support.
For building owners and operators: confidence over the whole life of the asset
zencontrol cloud provides a long-term approach to lighting control, rather than a single point-in-time installation.
- No dependence on one ageing PC hidden in a riser.
- Access, user changes and configuration are centrally managed.
- Supports staff changes, refurbishments and tenancy shifts without losing control.
- Helps keep your building aligned with evolving cyber requirements.
Frequently asked questions
We already have a local lighting PC. Why move to zencontrol cloud?
Local PCs are cheap to install but expensive to own in the long run. They must be patched, backed up, secured and eventually replaced – usually outside normal IT processes. zencontrol cloud removes that burden, centralises management and reduces the chance that lighting control becomes an unmanaged security risk.
What happens when staff or contractors leave?
With zencontrol cloud, access is tied to individual user accounts and roles. When a person no longer needs access, their account can be revoked without changing site-wide passwords or reconfiguring the system.
How does this help with insurance and compliance?
Many policies expect that systems exposed to the network are supported, updated and protected with user authentication. A cloud-managed control platform aligns far better with these expectations than an unmaintained legacy PC, helping reduce arguments about coverage if a cyber event occurs.
Can IT still control how the building network is used?
Yes. zencontrol cloud is designed to work with standard network practices. It removes the need for uncontrolled remote desktop tools and legacy servers, making it easier for IT to review, approve and secure the solution.
Make lighting control the strongest, not the weakest, link.
The risks in traditional lighting control systems are real: shared passwords, unpatched PCs, open remote access and missing backups. zencontrol cloud is designed specifically to remove these issues and give all stakeholders confidence over the life of the building.


